 If you have ever had your site hacked, you know it is a pain to clean up the mess – usually in the form of spammy high value keywords and links – as well as fix whatever compromise led the hackers to gain access to compromise your site in the first place. But there is also something else that webmasters should be concerned about – hackers also adding themselves as owners of the site in Google Search Console. And this can lead to a whole new set of headaches Securi has discovered.
If you have ever had your site hacked, you know it is a pain to clean up the mess – usually in the form of spammy high value keywords and links – as well as fix whatever compromise led the hackers to gain access to compromise your site in the first place. But there is also something else that webmasters should be concerned about – hackers also adding themselves as owners of the site in Google Search Console. And this can lead to a whole new set of headaches Securi has discovered.
When a hacker compromises a site, it isn’t that difficult to add the site to a spam Google Search Console account and upload the verification file, since many exploits allow the hackers to upload all manner of content and files. After all, there is a treasure trove of information within a Google Search Console account that could be used nefariously by spammers.
Using information in Google Search Console, they can see when their spam seems to be “caught” by Google, by seeing the search query referrals dropping off, with a dropping of indexed count or with a manual action warning in the account. This would allow a spammer to test a wide range of spam techniques on a mass scale, backed with an army of Search Console logins to track the health of the site.
It could also be used by hackers to test spammy links to see which ones seem to trigger link related manual actions, or to see how “thin” content can be before it trips content related manual actions. And all done without having to create sites at all, but by using compromised ones instead.
Hackers are not only using Google Search Console access to see traffic and stats related to the site, but are also using it to quickly submit sitemaps in order to get their spammy pages indexed or compromised pages reindexed much faster than merely waiting for Googlebot to discover them during crawling. When a hacker compromises your site, they want to maximize the amount of time those pages are indexed before the site owner discovers it and cleans it up. Being able to submit the pages created after your site was compromised, they are ensuring they get the most benefit while their content is on the site. After all, they have no idea if it will be removed the next day or the next year, and spammers don’t tend to be in the business of site longevity.
And of course, there are other things hackers can do within Google Search Console to your site if they want – such as deindex the site, remove specific pages and of course, unverify those on the account legitimately.
How do you know if hackers have added themselves to your accounts? Google does email site owners to let them know. The alert Google sends to site owners when another person is added to the account via Google Search Console is a WNC-582900:
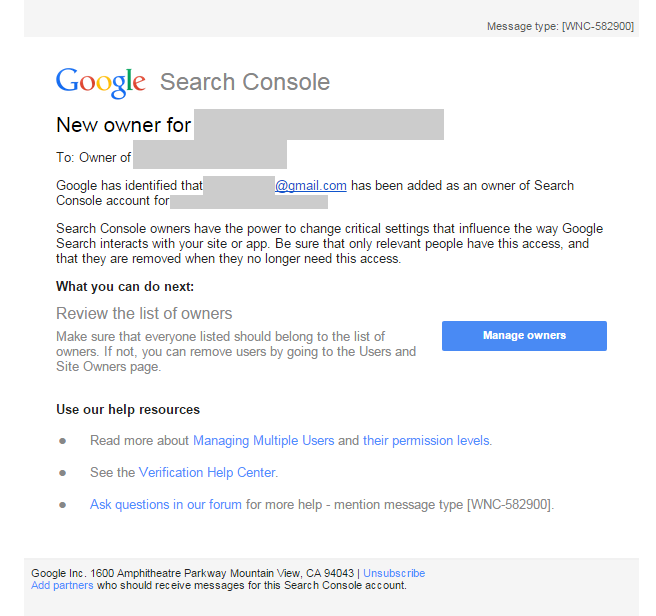 Which is another reason it is important to ensure your email address attached to your Google Search Console account is not only an active email address but one that is checked regularly.
Which is another reason it is important to ensure your email address attached to your Google Search Console account is not only an active email address but one that is checked regularly.
It also shows up in your account, where you can also unverify these accounts, but note you do need to remove the verification site for those accounts prior to doing this. While these files are generally placed in the root and are fairly obvious, they can also be hidden elsewhere on the site via .htaccess, making it trickier to spot.
Securi blog has noticed an increase in the number of compromised sites that have also seen Google Search Console accounts being added and verified while the site is hacked, and has a great deal more on these unauthorized site owner additions after a site has been hacked and what is being done with it. It is well worth the read, especially if you think any of your sites have been targeted with this.
Jennifer Slegg
Latest posts by Jennifer Slegg (see all)
- 2022 Update for Google Quality Rater Guidelines – Big YMYL Updates - August 1, 2022
- Google Quality Rater Guidelines: The Low Quality 2021 Update - October 19, 2021
- Rethinking Affiliate Sites With Google’s Product Review Update - April 23, 2021
- New Google Quality Rater Guidelines, Update Adds Emphasis on Needs Met - October 16, 2020
- Google Updates Experiment Statistics for Quality Raters - October 6, 2020
[…] Watch for New Owner WNC-582900 Google Search Console Alerts after Site Hacking, thesempost.com […]